Recenty the FBI warned that cyber thieves are finding ways around multifactor authentication protections. We may not own crypto accounts, but universities across the UK have implemented forms of two or multi-factor authentication to protect our accounts and we are grappling with strategies to ensure accessible forms for verification are available. The W3C WCAG Cognitive and Learning Disabilities Task Force has published an Accessible Authentication (User Story) to illustrate the need for the cognitive function test mentioned in the previous blog. It also highlights how memory impairments and difficulties with executve function can make MFA a challenge as well as time constraints.
There was a Twitter stream in February 2021, that highlighted more reasons why some of the MFA choices offered may not be helpful to individuals with Autism and Attention Deficit Hyperacive Disorder (ADHD). Devon Price’s insight into the frustrating nature of these extra levels of security illustrates the cognitive overload that can occur when several tasks have to be completed with multiple devices or systems.
I gotta say it. Multi-factor authentication is super inaccessible if you have disabilities that make it hard to switch between a bunch of applications and fill out forms, like Autism and ADHD, or if you're poor with inconsistent cell phone service or wi-fi access!
— Typer Durden (@drdevonprice) February 12, 2021
If you do not have an external code device, the choices tend to centre around the use of a personal mobile phone. Having checked the websites of 50 universities it appeared that 42 (84%) advised students to use an authenticator app – usually Microsoft, that also offers a Self Service Password Reset. Other options were the Authy, Google, Sophos or Duo apps. All the university systems still require the user to remember passwords with the extra verification and then encourage a back up option via SMS, a phone call and some mentioned a landline or email. Only 4 universities offered a choice of two authentication apps and just 7 mentioned the use of a fob or external device, although one said this would not to work with Virtual Personal Networks. Preference for Authy as an alternative was mentioned in a question about the Microsoft Authenticator, as this can be used on a desktop computer. At the time of writing Microsoft Authenticator instructions do not mention a desktop verification option to their MFA.
Some universities in the small study used the Microsoft instructions, but when searching for support it took well over 3 clicks, to find out about the authentication options offered by 14 out of the 50 universities (28%), 9 of these websites either had no information or required a log in. This meant that a new student may have no way of preparing for this aspect of registration, although all of the websites had good connections to their student support or IT services.
Only one university appeared to depend on a memorable word for verification and the use of authenticator apps usually meant that the code could be used without an internet connection or a connection to a mobile network provider. This does not mean that copying a code results in successful verification on all occasions.
Where concentration or attention is an issue, as may happen with ADHD, the problem of copying codes from one device to another can become worse as more attempts are made. Too many tries leads to lockout, desperation and yet another feeling of failure, let alone time wasting and other more severe consequences, if the actions are related to banking. Actions that involve recognition and copying qualify under the W3C WCAG cognitive function test as requiring an alternative method.
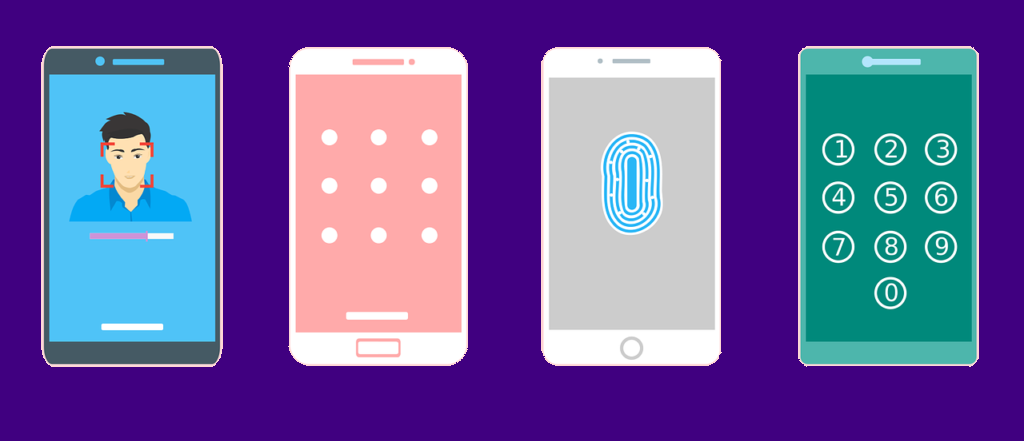
Using biometrics is often considered a good alternative, but it is not always easy to get facial recognition to work on phones if you are blind or have dexterity difficulties and some individuals really do not like sharing their facial image. The UK National Cyber Security Centre admits that fingers prints are not always recognised if people have been working in some industries or you are elderly and even a skin condition can cause problems. Also not all devices offer the chance of using finger recogntion.
In summary Making Content Usable for People with Cognitive and Learning Disabilities suggests four options:
- Web Authentication: An API for accessing Public Key Credentials [webauthn-2].
- Single Sign-on (SSO) that allow users to access many sites with a single login (federated login).
- Two step authentication with Bluetooth links (no copying).
- Quick Response Codes (QR Code).
The use of authentication apps, with a set up of 5 additional choices was offered by 6 of the 50 universities reviewed, so they provided more than the above options, plus the ability to use a helpline. When checking the helplines it became clear that there were often rather a lot of questions surrounding the Microsoft Authenticator, as evidenced by the University of Hertfordshire’s comprehensive set of answers. So It appears there is still much to do to make the process more inclusive.

